Custom security solution development
Our Cyber Security Experts can tailor Cyber Security Solutions for your business to ensure that your system is safe from any threats, attackers, or other kinds of vulnerabilities.
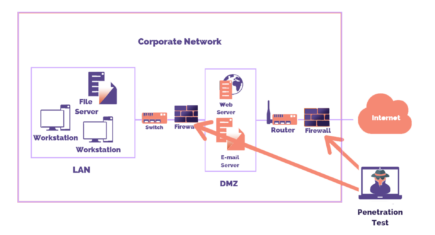
External Pentesting is a critical component of cyber security operations. Ethical hackers simulate real-world attacks from outside a company’s network to identify vulnerabilities in external-facing systems. By doing so, organizations can strengthen their security defenses, safeguard against data breaches, and prevent unauthorized access attempts.

Internal Pentesting includes authorized examination of an organization’s internal network, systems, and apps to spot vulnerabilities. Ethical hackers from a top Cyber Security Company mimic real-world attacks from within the network to address weaknesses and boost cybersecurity, ensuring strong protection against potential threats.
Our Cyber Security service conducts thorough wireless penetration tests to assess the robustness of security measures preventing unauthorized access. By exploiting wireless vulnerabilities, we identify and address risks such as unauthorized access to private SSIDs or privilege escalation on guest SSIDs, ensuring the integrity of your network defenses.
Mobile devices and software are essential, simplifying and enhancing our daily lives. Hackers often target them due to the data they handle. From banking to healthcare, organizations use mobile apps creatively. Managing security risks is challenging due to daily vulnerability discoveries. As a leading cyber security company in India, we specialize in Mobile Application Pentesting, ensuring robust protection for your mobile apps against evolving threats.

A Web application (Web app) is a program stored on a remote server, accessible over the Internet through a browser. Web services, handling sensitive data like user and financial information, are often cybercriminal targets. As web apps grow in complexity, the number of exploitable vulnerabilities is increasing over time. With increasing complexity, a Security Operations Center (SOC) is vital to mitigate rising exploitable vulnerabilities in web apps.

In the realm of cybersecurity, we, as a leading Cyber Security Company in India, uphold rigorous confidentiality standards and adhere to industry-leading practices to protect your sensitive information. Additionally, we take the extra step of signing non-disclosure agreements (NDAs) to guarantee the utmost safeguarding of your business data.
Our Cyber Security Experts can tailor Cyber Security Solutions for your business to ensure that your system is safe from any threats, attackers, or other kinds of vulnerabilities.
With a strong team of Cyber Security Specialists, develops a robust access management system and operates a Security Operations Center to ensure secure business data.
We offer Cyber security Specialists for hire to establish a user-identity and control management system, along with other Cyber Security Solutions, ensuring complete security for your business.
Enhance your system’s defenses with tailored cybersecurity services from a leading cybersecurity company in India, receiving custom configurations that align with your business requirements, address security needs, and guarantee comprehensive protection.
